Protecting Your Business from a Ransomware Attack
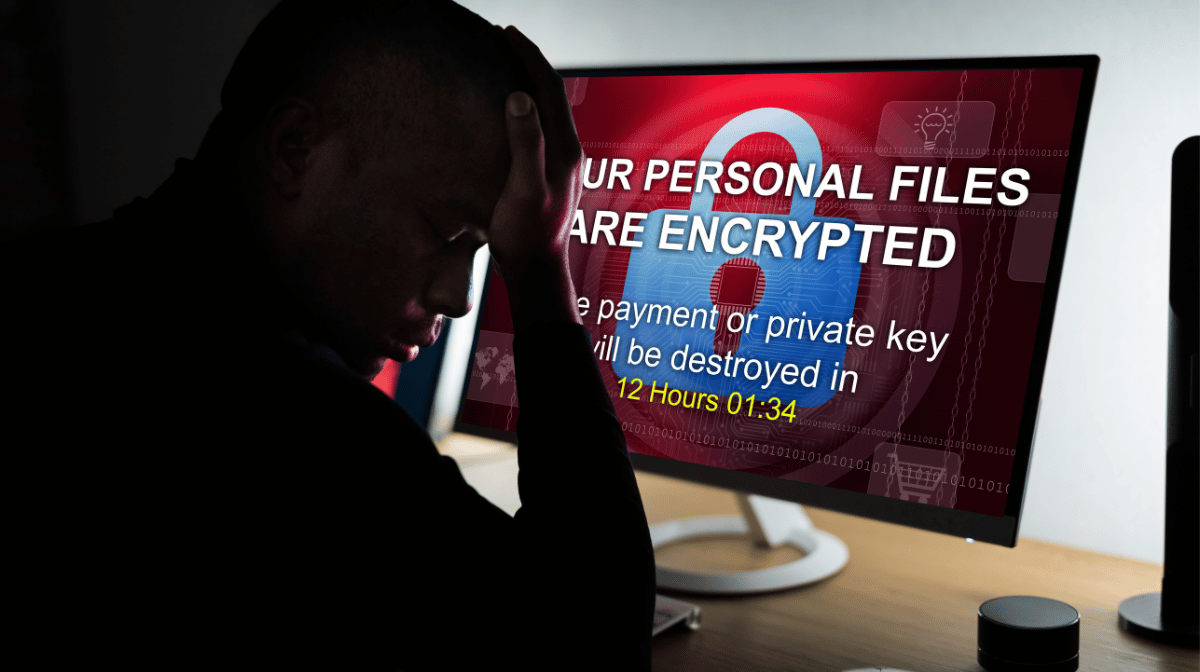
National headlines about ransomware attacks crippling Baltimore City and Cleveland Hopkins International Airport might leave smaller businesses thinking that governments and large corporations are the only entities facing a real threat of attack.
However, threats against businesses of all sizes have been on the rise. Malwarebytes Labs issued a Cyber Crime Tactics and Techniques 2019 Q1 Report stating that cyberattacks on businesses in general have increased 235% in the past year. Ransomware specifically is gaining rapid momentum in Q1 2019 with a 195% increase in ransomware attacks on businesses from Q4 2018 to Q1 2019.
What Makes Ransomware Different from Other Cyberattacks?
Ransomware is unique because it doesn’t need to target personal or sensitive information to be effective. The data must simply be valuable enough to the victim that they would consider paying the ransom to regain access to the data. While it’s true that ransomware also compromises sensitive data, its primary purpose is to paralyze the victim enough that they would pay the requested ransom. This is a particularly effective way of attacking businesses that are faced with the cost of paying employees who are unable to work and turning away customers when the business can’t deliver services, access information, and/or accept payments.
There are several best practices businesses should implement to protect themselves from ransomware, or really any cyberattack.
They include:
- User Education
- Firewall & Intrusion Detection/Protection
- Email & Web Filtering
- Security Software
The reality of ransomware is that it usually gets past these prevention efforts and enters a network when an end user inadvertently grants it access by opening a malicious email and/or clicking on a malicious link. This risk is mitigated through email safety awareness training and email filtering, but as these phishing attempts become more sophisticated it is becoming increasingly difficult for end users to accurately identify all malicious emails.
Is it Cheaper to Just Pay the Ransom?
It’s tempting to pay the ransom when an attack makes its way past all your prevention efforts and holds your network and data hostage. When you compare the cost of paying employees who can’t work and losing business both during downtime and due to future reputation damage, it might seem to make financial sense to pay an average ransom request of around $6,000. However, one in every five companies that pay the ransom does not receive the decryption key, and in many cases, companies are hit repeatedly.
The only surefire way to combat a ransomware attack is to adopt an effective Backup and Disaster Recovery (BDR) strategy. The key to an effective BDR strategy is aligning it with the amount of data your business is at risk of losing at any given time and the amount of downtime your business could tolerate while your data is restored from backup.
Am I Safe From Ransomware if My Data is Backed Up?
Yes, and no. It's true that a functioning backup solution allows you to restore data, but it can often take days or weeks to fully restore operations from certain types of backup solutions. Not to mention, many backup solutions charge little to nothing to store your data, but will cost you significantly in downtime and labor to recover and restore your systems to full functionality.
In this video, Innovative, Inc.'s VP of Operations, Tyler Snyder, walks you through a case study of one business that survived two back-to-back ransomware attacks. In both instances, the business had a fully functional backup solution in place. However, the first attack resulted in three full days of downtime. Immediately following that attack the business adopted a different backup and disaster recovery strategy. When the business was hit again they were only down for about one hour thanks to a backup solution more in line with the business’ tolerance for downtime.
What Type of Backup Offers the Best Protection Against Ransomware?
The best defense against ransomware, or really any cyberattack, as an image-based, hybrid backup solution.
Image-Based Backups
Image-based backups take a snapshot of your entire server or device, allowing you to almost instantly restore full functionality. Other types of backup are file based, which means individual files are transferred to the backup device, either locally or in the cloud. Restoring from a file-based back up requires a significant amount of time to individually download multiple files, and reinstall and reconfigure all software and application settings.
Hybrid Backups
Hybrid backup solutions include backup to a local device and to the cloud. The local device allows for more frequent and faster backup speeds, and the cloud allows you to restore your data in cases where a local event like a flood or fire damages the local device.
Other Characteristics of a Quality Backup Solution
In addition to the speed and redundancy of image-based, hybrid backups. Look for the following characteristics from any backup provider.
- Encryption - Data should be encrypted by AES-256 bit encryption during transport, storage, and replication. This ensures that no third party can access your data after it leaves your network.
- Redundant Data Centers - In addition to the redundancy offered by backing up data to both a local device AND to the cloud, cloud backup providers should house your data in at least two data centers located in different geographic locations.
How Will I Know What Backup and Disaster Recovery Solution is Right for My Business?
There are many cyber threat prevention and disaster recovery strategies available, and almost every solution has its place. The key to protecting your business is implementing a solution that mitigates your unique risks and protects your network and data in a way that allows you to maintain business continuity. This is why your IT team should understand your business and work with you to implement the right solutions for your unique situation. Your IT team could be an internal staff resource, an outsourced IT partner or managed service provider, or a combination of an internal staff member working together with a vendor.